Website Hacking Most Common Techniques
Almost every human on this earth commonly know what website is and might be 5 percent of people on earth have a website that they manage. Based on current data, by 2020 there are around 1.24 billion websites in the world. Of the many websites, there are still many who do not realize that there are many loopholes to steal or enter without permission to the website, even for professional level developers. This time we will discuss the techniques most often used by hackers to hack websites.
What is a Web Application? And What Are The Types Of Threats To The Website?
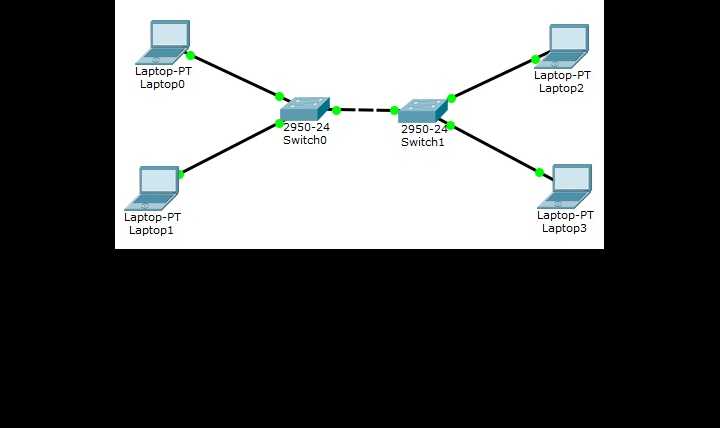
Basically a Web application is an application based on a client-server model. The server provides database access and business logic. The website will be hosted on the server by running web services while the client application runs on a web browser such as Mozilla/Chrome. Web applications are usually written using a specific programming language such as PHP/Java-Script, while the most popular database engines are Oracle, PostgreSQL, MySQL, etc.
Then how do hackers attack the websites that we manage? Depending on what technique the hacker penetrates. They can do this by exploiting bugs from the hardware / software infrastructure platform or the logic of your website programming.
Common Techniques Hackers Use For Website Hacking are
- SQL Injection: The purpose of this technical threat is to bypass login algorithms, sabotage data, etc. Basically this technique attacks and exploits our website database system based on SQL.
- DOS/Denial of Services: Basically, this technique is to sabotage user and user access to the website we manage, the most common way is to flood the website / server with useless access so that when a valid transaction from a user enters it cannot be processed because the server is slow due to being flooded with unsustainable traffic. useful by the hacker.
- Cross Site Scripting XSS: The main purpose of this technique is to be able to inject executable code in the browser on the client side. Usually hackers will attack pages or pages that contain forms for users and look for loopholes of logic on the form's website. The most common purpose is to steal session cookies from valid users by posing as victims so that they can get sensitive data from the victim.
- Cookie/Session Poisoning: The main purpose of hackers using this technique is to modify cookies or session data to gain unauthorized access. Usually this is due to the lack of validation methods on the forms used by users so that hackers can exploit them.
- Form Tampering: In this way, hackers usually modify form data such as prices in e-commerce applications so that hackers can get goods at lower prices.
- Phising: This technique is usually used by hackers to attack ordinary users, usually they attack via email by inserting malware or sending a url similar to a website that is commonly used by users, for example klikbca.com and then converted by the hacker to klikbcaa.com. Users will see the exact same appearance of the website there, but when the user gets stuck on the hacker's website, they will unconsciously give their confidential data for free to the hacker


 English
English